Organizations worldwide now prioritize the protection of containerized workloads as they expand their digital presence across diverse cloud platforms. This specialized guide analyzes the Certified Kubernetes Security Specialist (CKS), a top-tier credential for professionals who must safeguard production clusters against complex cyber threats. Whether you operate as a platform engineer or a security lead, mastering these defensive protocols remains vital for high-level career advancement. This roadmap simplifies your transition from general cluster management to expert-level security orchestration. Ambitious candidates often seek structured training through DevOpsSchool to bridge technical knowledge gaps and sharpen their practical skill sets.
What is the Certified Kubernetes Security Specialist (CKS)?
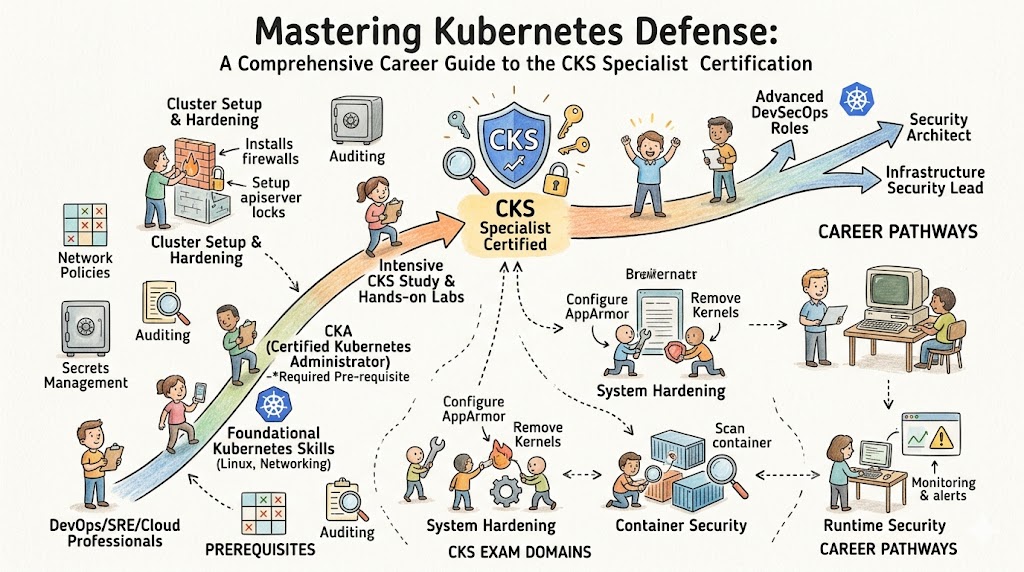
The Certified Kubernetes Security Specialist (CKS) serves as a rigorous, performance-based validation of an engineer’s ability to protect containerized applications throughout the entire lifecycle. Candidates demonstrate their proficiency by securing the build, deployment, and runtime phases within a live, proctored command-line environment. This certification emphasizes hands-on cluster hardening over abstract theory, reflecting the high-stakes demands of modern enterprise infrastructure. By focusing on the broader ecosystem—including host-level security and supply chain integrity—it ensures that specialists can mitigate real-world vulnerabilities effectively.
Who Should Pursue Certified Kubernetes Security Specialist (CKS)?
DevOps professionals and system administrators who already hold a valid CKA credential find this specialization particularly impactful for their career trajectory. Site Reliability Engineers (SREs) also gain immense value, as they acquire the tools to ensure infrastructure resilience and data protection in volatile environments. In both the Indian and global markets, organizations actively hunt for architects capable of implementing Zero Trust frameworks. Even technical directors pursue this path to deepen their understanding of risk mitigation within the modern software supply chain.
Why Certified Kubernetes Security Specialist (CKS) is Valuable and Beyond
Enterprises demand a “security-first” architecture as they migrate mission-critical data to cloud-native environments. The CKS provides long-term value because it highlights fundamental security principles that outlast specific software versions or temporary industry trends. Achieving this status signals a high level of professional maturity and a dedicated commitment to safeguarding organizational digital assets. Ultimately, this investment positions professionals for premium roles in the DevSecOps and platform engineering sectors.
Certified Kubernetes Security Specialist (CKS) Certification Overview
The certification program operates via the official training portal and maintains a presence on DevOpsSchool. This specialized assessment tests a candidate’s competence through a proctored, hands-on exam that requires direct interaction with multiple Kubernetes clusters. The curriculum stays current with the latest releases, ensuring that practitioners apply the most relevant security configurations. This rigorous approach maintains the credential’s status as one of the most respected and sought-after honors in the cloud-native industry.
Certified Kubernetes Security Specialist (CKS) Certification Tracks & Levels
The ecosystem structures this certification as a specialist tier that builds upon foundation and professional tracks. It aligns seamlessly with the career trajectory of engineers moving from general administration to high-level security specialization. These tracks ensure that a candidate masters cluster operations before attempting to implement complex hardening strategies. Such a logical progression guarantees that specialists understand the operational constraints of the systems they protect.
Complete Certified Kubernetes Security Specialist (CKS) Certification Table
| Track | Level | Who it’s for | Prerequisites | Skills Covered | Recommended Order |
| Cloud Security | Specialist | Security Architects | Valid CKA | API Hardening, Runtime Defense | Step 3 |
| Platform Defense | Advanced | SREs, DevOps | Kubernetes Core | Network Policies, Secrets | Step 2 |
| DevSecOps | Professional | Cloud Engineers | Linux Expertise | Image Scanning, Auditing | Step 1 |
Detailed Guide for Each Certified Kubernetes Security Specialist (CKS) Certification
Certified Kubernetes Security Specialist (CKS) – Specialist Level
What it is
This credential confirms an engineer’s mastery over securing the build, deployment, and runtime aspects of Kubernetes. It validates that the holder can protect infrastructure from both external intrusions and internal misconfigurations.
Who should take it
Senior DevOps engineers and security analysts with significant container experience should target this exam. It suits those who manage high-compliance environments where data integrity is paramount.
Skills you’ll gain
- Hardening the API server and the underlying host operating system.
- Implementing strict Network Policies to control pod-to-pod communication.
- Deploying runtime security monitors like Falco to detect suspicious activity.
- Establishing automated vulnerability scanning within the container supply chain.
Real-world projects you should be able to do
- Design a multi-tenant cluster that utilizes strict namespace isolation.
- Configure Pod Security Admission to enforce organizational safety standards.
- Execute a comprehensive audit of cluster logs to identify unauthorized access.
Preparation plan
- 7-14 Days: Review the official documentation and familiarize yourself with the exam terminal.
- 30 Days: Build a local lab to practice host hardening and API flag configurations repeatedly.
- 60 Days: Deep dive into third-party utilities like Trivy, Falco, and OPA Gatekeeper for advanced defense.
Common mistakes
- Forgetting to update the context when moving between different cluster tasks.
- Spending excessive time on complex, low-point questions during the timed exam.
- Ignoring host-level security tasks such as kernel module management or SSH hardening.
Best next certification after this
- Same-track option: Advanced Cloud Security Professional
- Cross-track option: Certified Kubernetes Application Developer (CKAD)
- Leadership option: Certified DevSecOps Manager
Choose Your Learning Path
DevOps Path
The DevOps path integrates security directly into the automated CI/CD pipeline. Professionals learn to trigger security scans the moment a developer commits code, preventing vulnerabilities from reaching production. This route emphasizes the synergy between rapid delivery and infrastructure safety. It perfectly suits those who build and maintain modern software delivery engines.
DevSecOps Path
This track evolves the standard DevOps workflow by placing security at the core of every operation. Candidates treat security policies as version-controlled code, ensuring every change remains auditable and transparent. You will utilize admission controllers and automated compliance frameworks to maintain a constant state of readiness. Most CKS holders choose this path to lead organizational shifts toward proactive defense.
SRE Path
Site Reliability Engineers explore the intersection of cluster security and service availability. This path highlights how security incidents or configuration drifts can compromise system reliability. You will build resilient clusters that alert operators during security events while maintaining high uptime. This specialization remains critical for services operating in highly regulated industries.
AIOps Path
Engineers in the AIOps path leverage machine learning to identify anomalies in cluster behavior that might suggest a breach. This involves processing vast amounts of log data to uncover patterns that bypass human observation. This route serves those working at a massive scale where manual monitoring proves ineffective. It merges data science with infrastructure security for a modern defense.
MLOps Path
The MLOps path secures the specialized pipelines used to train and deploy machine learning models on Kubernetes. Professionals learn to protect sensitive datasets and secure model serving endpoints against injection attacks. As AI adoption grows, protecting the underlying compute infrastructure becomes a vital skill set. This niche offers high growth for security experts interested in artificial intelligence.
DataOps Path
DataOps professionals protect the data pipelines running within Kubernetes to meet strict privacy regulations. This involves managing secrets for database access and encrypting data-in-transit across microservices. It is a fundamental role for any organization handling high-volume personal or financial information. This path ensures that data remains the most secure asset within the infrastructure.
FinOps Path
The FinOps path investigates how security choices affect cloud expenditures and resource efficiency. For instance, running intensive security agents can bloat cloud bills if not optimized correctly. This path helps practitioners balance a strong defense with a lean budget. It represents a strategic role for those managing both technical security and financial health.
Role → Recommended Certified Kubernetes Security Specialist (CKS) Certifications
| Role | Recommended Certifications |
| DevOps Engineer | CKS, CKAD |
| SRE | CKS, CKA |
| Platform Engineer | CKS, Cloud Architect |
| Cloud Engineer | CKS, Network Expert |
| Security Engineer | CKS, Pen-Test Specialist |
| Data Engineer | CKS, Data Security |
| FinOps Practitioner | CKS, Cloud Economics |
| Engineering Manager | CKS, Leadership Track |
Next Certifications to Take After Certified Kubernetes Security Specialist (CKS)
Same Track Progression
Deepen your expertise by pursuing provider-specific security credentials after mastering Kubernetes security. Focus on exams like the AWS Certified Security or Google Cloud Professional Security Engineer. These certifications allow you to apply your container knowledge to the wider cloud ecosystem. Maintaining this focus keeps your skills at the cutting edge of defensive technology.
Cross-Track Expansion
Broaden your perspective by exploring application development or data engineering tracks. Earning a CKAD, for example, helps you understand how developers interact with the platform, leading to better security policy design. This versatility prevents technical silos and fosters a culture of shared responsibility. Expanding your reach makes you a more valuable asset to any cross-functional team.
Leadership & Management Track
Transition toward strategic oversight by pursuing leadership certifications in IT service management or DevSecOps. You will focus on building security cultures, managing departmental budgets, and defining long-term infrastructure goals. This track suits those who wish to influence organizational direction rather than focusing solely on implementation. It bridges the gap between technical execution and executive strategy.
Training & Certification Support Providers for Certified Kubernetes Security Specialist (CKS)
DevOpsSchool provides a robust and hands-on training program that engineers worldwide respect for its practical approach. Their experts lead live sessions that tackle real-world production issues, ensuring students gain actionable insights. The curriculum evolves alongside the official exam, providing the most current knowledge available. Learners enjoy extensive lab access and a supportive community that fosters professional growth.
Cotocus delivers customized training solutions for corporate teams looking to strengthen their cloud-native defense capabilities. They host high-intensity workshops that simulate attack vectors and defensive responses. Their personalized mentorship ensures high success rates for professional teams.
Scmgalaxy offers a treasure trove of community resources, including detailed blogs and practice scenarios for security aspirants. It functions as a central hub for the DevOps community to share open-source security best practices.
BestDevOps prioritizes lab-based learning through high-quality certification prep courses. Their instructors bring decades of industry experience to help students navigate the complexities of Kubernetes security.
devsecopsschool.com focuses exclusively on the cultural and technical intersection of development and security. They offer specialized tracks that encourage engineers to build security into every layer of their infrastructure.
sreschool.com caters to the needs of Site Reliability Engineers by offering courses that blend security with system performance and uptime requirements. Their courses target those who manage large, high-availability clusters.
aiopsschool.com explores the future of infrastructure by teaching engineers to integrate AI into their operational workflows. They offer modules on automated incident response and proactive threat detection.
dataopsschool.com addresses the unique security challenges found in big data platforms on Kubernetes. Their training helps data engineers maintain compliance and data integrity at scale.
finopsschool.com educates professionals on the financial impact of their technical security decisions. They provide strategies for maintaining a robust defense without exceeding cloud budgets.
Frequently Asked Questions (General)
- How much more difficult is the CKS compared to the CKA?
Most candidates find the CKS significantly more challenging because it requires deep expertise in third-party security tools and host hardening. While the CKA tests operations, the CKS demands high-level defensive skills.
- Does the Linux Foundation require a CKA before taking the CKS?
Yes, you must hold a valid Certified Kubernetes Administrator (CKA) certification before you can attempt the CKS. This prerequisite ensures that all security specialists already understand core cluster operations.
- What is the typical validity period for this credential?
The certification remains active for two years. You must retake the exam or follow established renewal protocols to maintain your status as an active Kubernetes security specialist.
- Which resources can I access during the actual exam?
You may use specific official documentation pages from the Kubernetes and security tool websites during the test. However, you must navigate these quickly to stay within the strict time limits.
- Is a theoretical study plan sufficient to pass the CKS?
No, you will likely fail without extensive hands-on practice. The performance-based exam requires you to configure security settings and troubleshoot live issues within a Linux terminal.
- What score must I achieve to pass?
The passing score generally sits around 67%, although the Linux Foundation may adjust this based on the exam version. Speed and accuracy remain the most critical factors for success.
- How many minutes do I have to finish the exam?
The exam provides exactly 120 minutes to complete all required tasks. Successful candidates manage their time efficiently, focusing on high-value questions first.
- Where does the exam take place?
The exam occurs in a remote-proctored, browser-based Linux environment. You interact with multiple pre-configured Kubernetes clusters to resolve various security scenarios.
- Will this certification impact my salary expectations?
Recruiters often offer higher compensation to security-focused engineers due to the specialized nature of the CKS. It serves as a strong differentiator for senior and lead engineering roles.
- Can I retake the test for free if I fail?
Most exam purchases include one free retake attempt. This policy allows you to learn from your first experience and adjust your preparation accordingly.
- Do I need to understand Linux kernel security?
Yes, a solid foundation in Linux security—including syscalls, kernel modules, and permissions—helps immensely. The CKS often requires tasks that occur at the host level rather than the API level.
- Which security tools should I prioritize during my labs?
Focus your practice on Falco, Kube-bench, Trivy, and OPA Gatekeeper. Understanding how to integrate and configure these within a cluster is essential for passing.
FAQs on Certified Kubernetes Security Specialist (CKS)
- What specific domains does the CKS exam cover in depth?
The curriculum focuses on Cluster Setup, Hardening, System Security, Vulnerability Minimization, Supply Chain Security, and Runtime Monitoring. Each area requires practical implementation skills.
- How often does the Linux Foundation update the exam version?
The exam version typically updates to match recent stable releases of Kubernetes. Always check the current version before you finalize your study plan or lab environment.
- Does the CKS training align with global compliance standards?
Yes, you learn technical controls that help meet requirements for HIPAA, PCI-DSS, and SOC2. The course covers the auditing and isolation necessary for formal compliance.
- Can I use my own handwritten notes during the test?
No, the exam strictly prohibits personal notes, books, or external websites. You may only use the pre-approved official documentation links provided within the exam interface.
- Why does the CKS emphasize host-level security so heavily?
A cluster remains vulnerable if the underlying nodes lack proper defense. Compromising the host allows an attacker to bypass many Kubernetes protections, making host hardening critical.
- What lab setup do you recommend for preparation?
Setting up a multi-node cluster using Kubeadm provides the most realistic practice. You should also use simulation platforms to improve your speed in a timed environment.
- Does the exam test cloud-specific tools like AWS GuardDuty?
The CKS remains platform-agnostic and focuses on native Kubernetes features and open-source tools. While it doesn’t cover cloud-specific services, the skills transfer easily to any provider.
- Is the CKS widely recognized in the enterprise tech sector?
Global technology firms and major cloud providers highly value this credential. it provides an objective measure of an engineer’s ability to maintain secure, enterprise-grade infrastructure.
Final Thoughts: Is Pursuing the CKS Worth Your Effort?
Obtaining your CKS accreditation is a significant career achievement that makes you an active protector of cloud-native infrastructure. The capacity to create and protect secure systems continues to be a crucial advantage in a time of growing cyberthreats. The ensuing professional opportunities and technological maturity make the discipline and substantial technical effort required for this journey worthwhile. You will put yourself at the forefront of the field if you concentrate on developing practical mastery rather than merely obtaining the credential.